| Universal Advanced Solutions
System Integrator Applications
Security & Intelligence Applications
Hardware Products
Software Products
Military
-
The modern military operations need, the usage and exploitation of the RF spectrum.
-
CRFS approach the Cyber and Electromagnetic Activities.
-
Spectrum capacity is a finite resource, & which need monitoring & managing

Electronic Warfare Support
-
SIGINT (Signal Intelligence), which may be COMINT or ELINT.
-
How to extract, classify and locate transmissions within the signal spectrum.
Strategic Use:
-
Monitoring the utilization of emitters.
-
Developing any future offensive or defensive operations.
Tactical Use
-
Real-time spectrum intelligence.
-
Raising the instant awareness of the troops.
For more info: https://www.crfs.com/applicationstory/increasing-sigint-capabilities/

Battlefield Situational Awareness
-
Deliver a clearer battlefield picture.
-
Pick up RF transmissions over a wide bandwidth.
-
Radio silence (Radio silence)
-
Harmony cooperation between two friendly troops.
-
Avoid to be geolocated from the RF emissions of your RF equipment.
-
For more info: https://www.crfs.com/applicationstory/battlefield-situational-awareness/

Passive Aircraft Tracking
-
Radar is commonly used in tracking the aircraft’s location.
-
Tracking aircraft without alerting them to the fact that they are being tracked.
-
Determine Passively the aircraft’s location.
-
Detect The following:
-
Aircraft coordinates: Latitude, Longitude, Altitude, Course, Speed, Signal data
-
Signal Types: IFF, ADS-B, Link16, TACAN/DME, Radar, ATC channels
-
For more info: https://www.crfs.com/applicationstory/passive-aircraft-tracking-using-rf/

Naval EMCON (Emissions Control)
-
Selective control of EM’s usage, to optimize C2 capabilities
-
Avoid Detection by the enemy sensors.
-
Mutual interference among friendly systems.
-
Enhancing MILDEC Plan.
-
Protecting EID (Electrically Initiated Devices) from HERO (Hazards of Electromagnetic Radiation to Ordnance).
-
Avoid unauthorized or authorized cell phone emissions.
-
For more info: https://www.crfs.com/applicationstory/naval-emcon-emissions-control/

Proving Grounds & Test Ranges
-
The scenarios, strategy, forces and equipment need to be implemented
-
Efficient & effective testing on proving grounds, results in efficient, & effective performance in the war.
-
Avoid mutual EM interference.
-
For more info: https://www.crfs.com/applicationstory/securing-proving-grounds-and-test-ranges/

Interference hunting during UAV testing
Military UAV used for:
-
Navigation
-
Communications
-
situational awareness
-
Attacking & defending
Running Your Test Without Risk:
-
Testing your expensive UAV, with high confidence.
Reducing the damage budget
To avoid drone loss:
-
Monitoring RF spectrum, before and during UAV test runs.
-
Military and commercial source of interference, need to be identifiable
-
Monitoring wide range of frequencies, from VHF to SATCOM bands
For more info: https://www.crfs.com/applicationstory/interference-hunting-uav-test-and-operation/

Covert Spectrum Monitoring
Some environments are very harsh, to install a permanent structure for RF monitoring, like:
-
Hostile locations: contested borders, war zone, & terrorist zone.
-
Environmental challenges: cliffs, forests, swamps or dunes.
-
Rapid deployments: Detecting jamming, & Drones used in smuggling drugs, & weapons into prisons & borders.
-
Emergency: VIP visit, Sporting event.
-
For more info: https://www.crfs.com/applicationstory/configure-deploy-capture-retrieve/

Maritime Safety & Security
-
Sea border security responsibilities
-
Responding to vessels with problems
-
Collisions
-
Medical incidents at sea
-
Pollution control
Interference, due to:
-
Channels allocation unrespectable.
-
Uninformed users or foreign nationals
-
Intended interference on Mayday calls.
-
Carelessness

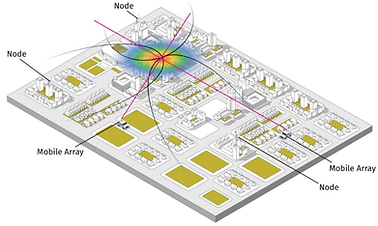
Border Monitoring
-
International borders can cover hundreds or even thousands of miles.
-
Impossible to secure every square mile of a border with a physical manned presence
-
A network of high-performance RFeye receivers can pick up RF spectrum transmissions.
-
A cell phone, VHF radio or other device can be detected, classified, & geolocated.
-
For more info: https://www.crfs.com/applicationstory/border-security
Regulatory
-
Managing the spectrum in more effective, & efficient way by Regulators.
-
EM spectrum is very valuable resource.
-
Used in: making phone calls, watching television, GPS navigation, & etc.
-
National regulators need to ensure, that the spectrum is uncongested & interference free.
-
As the number of “connected” devices increase, the pressure on the RF spectrum increasing, which increase the need of innovative ways to monitor and manage the spectrum.
Hybrid Geolocation
-
When it comes to geolocation performance, you don’t need to compromise.
-
AOA/TDOA are used for geolocation over wide areas.
-
For more info: https://www.crfs.com/applicationstory/hybrid-aoa-tdoa/

DF in urban environments
-
Direction Finding (DF) systems can often seem to fail, when used in the urban environment.
-
This problem can be attributed to multipath propagation.
-
Using the multiple Lines of Bearing (LOB) obtained as a single vehicle-mounted DF antenna array moves, to avoid multipath.
-
For more info: https://www.crfs.com/applicationstory/direction-finding-urban-environments/

Airport Interference
-
Communications, navigation systems and even Autoland systems can be impacted by RF interference at airports.
-
Preventing and quickly resolving interference at airports is essential for avoiding disruption, financial loss and serious accidents.
-
Engineers may be sent out to an airport over ten times with an portable RF monitoring and each time find that the interference source has been and gone.
-
Continuous RF monitoring solution isn’t only effective, but also cost effective.
-
For more info: https://www.crfs.com/applicationstory/resolving-rf-interference-airports/

Radar interference to MO
-
Radar interference to mobile operators.
-
Detecting and locating pulsed interference sources in real time.
-
Resulting in dropped calls, impaired voice quality and reduced data speeds
-
Noisy Neighbor’s interference at the country’s border
-
For more info: https://www.crfs.com/applicationstory/resolving-radar-interference-mobile-operators/

Portable Spectrum Monitoring
Some environments are very harsh, to install a permanent structure for RF monitoring, like:
-
Hostile locations: contested borders, war zone, & terrorist zone.
-
Environmental challenges: cliffs, forests, swamps or dunes.
-
Rapid deployments: Detecting jamming
-
Emergency: Sporting event.
-
For more info: https://www.crfs.com/applicationstory/configure-deploy-capture-retrieve/
System Integrator
Why work with CRFS?
-
Open architecture aids third-party integration
-
Proven field-ready, reliable hardware and software
-
Comprehensive documentation
-
Expert engineering support
-
Transparent, honest relationships

Electro-Optical Integration
-
Optical systems extend our own senses using superior optics and image enhancement.
-
They are able to identify and track drones based on their visual signature, and, when using infrared (IR), by a drone’s heat signature.
-
Optical systems give an unrivaled understanding of context. For example, by verifying if a drone is weaponized.
-
They do, however, still need additional hardware to perform geolocations and can encounter difficulty in coping with bad weather and bright sunlight.
-
For more info: https://www.crfs.com/integrated-dronedefense/

Acoustic Sensors Integration
-
Acoustic sensors are programmed to recognize the unique sounds produced by drone motors.
-
They rely on a library of sounds from known drones, so if a drone isn’t in the library, it won’t be detected.
-
Range from the target, background noise and strong winds can also influence the effectiveness of acoustic sensors.
For more info: https://www.crfs.com/integrated-dronedefense/
Security & Intelligence

Counter Surveillance
-
TSCM (Technical Surveillance Counter Measures)
-
The threats are real
-
Devices can be difficult to locate
-
Beyond bug sweeping
Used in:
-
Secure facilities
-
Embassies & diplomatic buildings
-
Commercial offices
-
Data centers
-
Banking and financial institutions
-
CNI (Critical National Infrastructure)
-
Combating Drones
-
For more info: https://www.crfs.com/counter-surveillance/





















